Tempest
This room aims to introduce the process of analyzing endpoint and network logs from a compromised asset. Given the artifacts, we will aim to uncover the incident from the Tempest machine. In this scenario, you will be tasked to be one of the Incident Responders that will focus on handling and analyzing the captured artifacts of a compromised machine.
Step 1 – Log Analysis Preparation
This part of the room is about prepping the logs for analysis. A quick run down of logs as well as event correlation
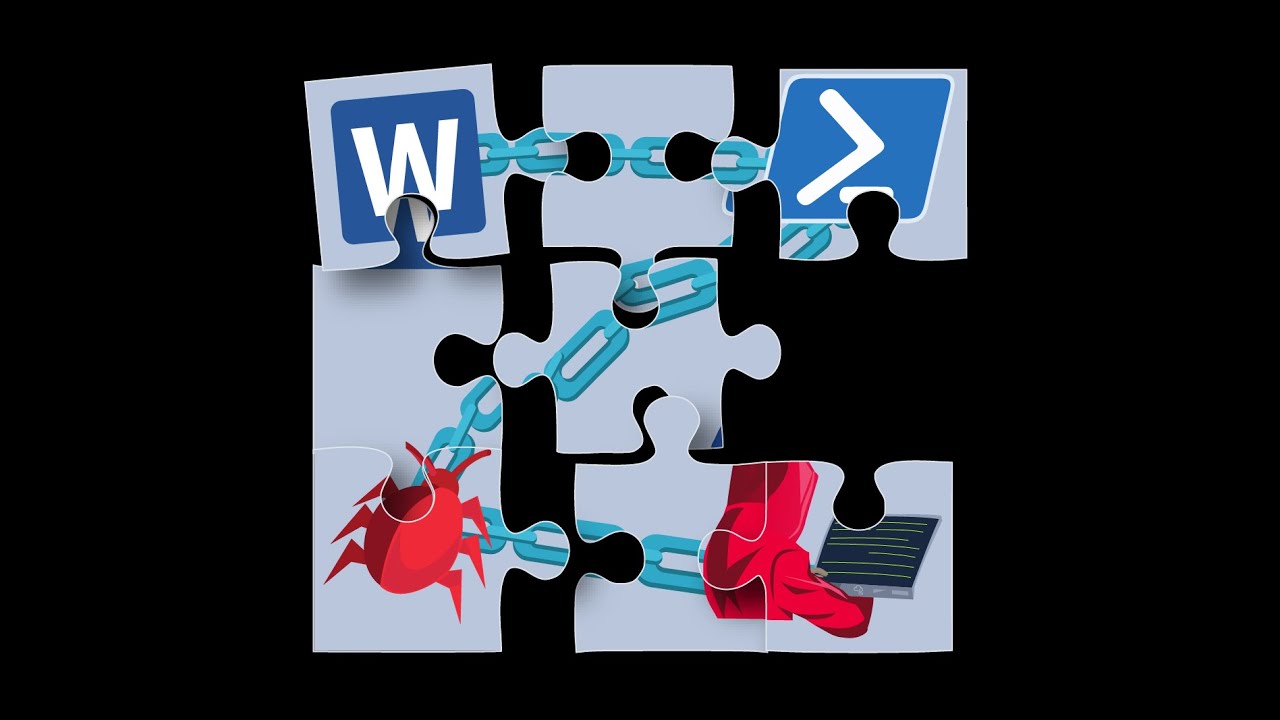
Using multiple data sources we can connect the following to an event. This will help us in “telling the story”
- Source and Destination IP
- Source and Destination Port
- Action Taken
- Protocol
- Process name
- User Account
- Machine Name
Step 2 – Tools and Artifacts